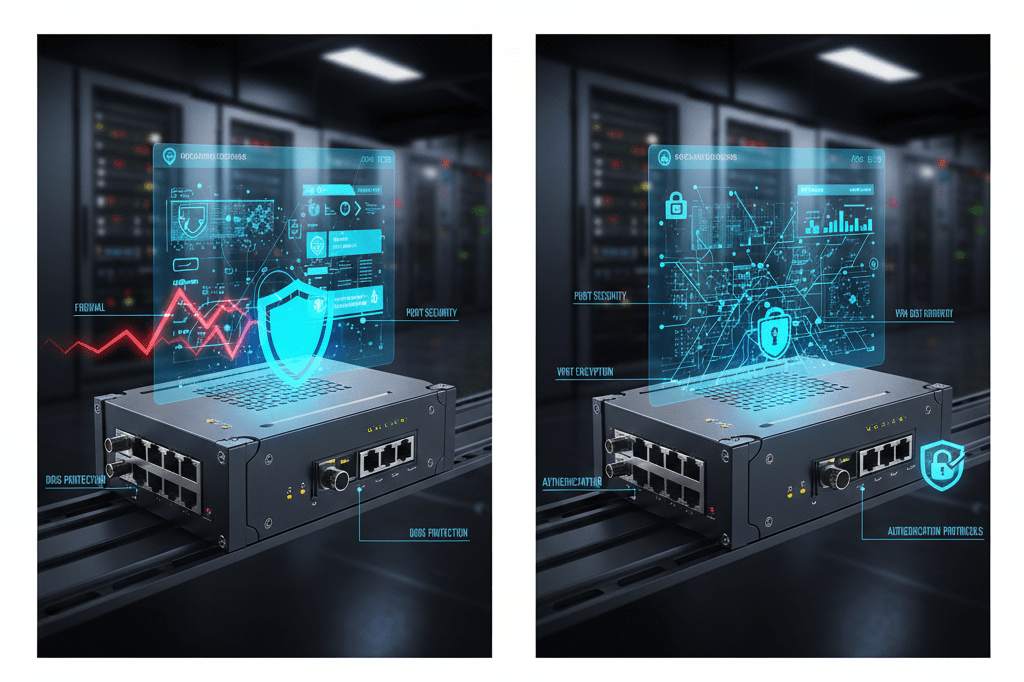
Cybersecurity Features Managed Industrial Ethernet Switch
Industrial networks face increasing cyber threats as OT systems connect to corporate networks and cloud platforms. Advantech managed industrial Ethernet switches with comprehensive cybersecurity features protect critical infrastructure from unauthorized access, malware propagation, and network attacks.
802.1X Network Access Control
802.1X authentication requires devices to authenticate before network access, preventing unauthorized equipment from connecting. RADIUS servers verify credentials, ensuring only approved devices join production networks. Guest VLANs quarantine unauthenticated devices for remediation.
Port Security and MAC Filtering
Port security limits devices per port preventing switch flooding attacks. MAC address filtering creates whitelists allowing only known devices. Dynamic learning identifies legitimate devices while blocking unauthorized connections. Violation actions include port shutdown, trap notifications, or traffic blocking.
Access Control Lists
ACLs filter traffic based on IP addresses, protocols, and ports. Rules block malicious traffic, restrict communication between network zones, and enforce security policies. Time-based ACLs change access during different shifts or maintenance windows. Logging monitors rule matches for security analysis.
Secure Management
HTTPS web interfaces, SSH command line access, and SNMPv3 encrypt management communications preventing credential theft. Certificate-based authentication verifies administrator identities. Role-based access control limits configuration abilities per user responsibilities. Audit logs track all administrative actions for compliance.
FAQ
Why do industrial networks need cybersecurity features?
Converged OT/IT networks expose industrial systems to threats: ransomware, unauthorized access, data theft, and sabotage. Security features limit attack surfaces, detect intrusions, and enforce access policies protecting critical infrastructure.
Do cybersecurity features affect network performance?
Modern switches implement security in hardware with minimal performance impact. ACL processing occurs at wire speed. Authentication introduces slight connection delays but doesn’t affect established communications. Properly configured, security enhances rather than hinders operations.